Microsoft Windows Xp Wanna Cry Patch Download
Microsoft issues ‘highly unusual’ Windows XP patch to prevent massive ransomware attack. But there are still organizations that continue to run Windows XP despite the risks. Microsoft is. A single point of Microsoft Windows patches for Wanna.Cry ransomware. I created this website as a single point for those who are trying to surf in the nightmare of Microsoft Update Catalog website and looking for patch their systems to protect from Wanna.Cry ransomware. Security Update for Windows XP SP2 for x64-based Systems. Given the potential impact to customers and their businesses, we made the decision to make the Security Update for platforms in custom support only, Windows XP, Windows 8, and Windows Server 2003, broadly available for download (see links below).
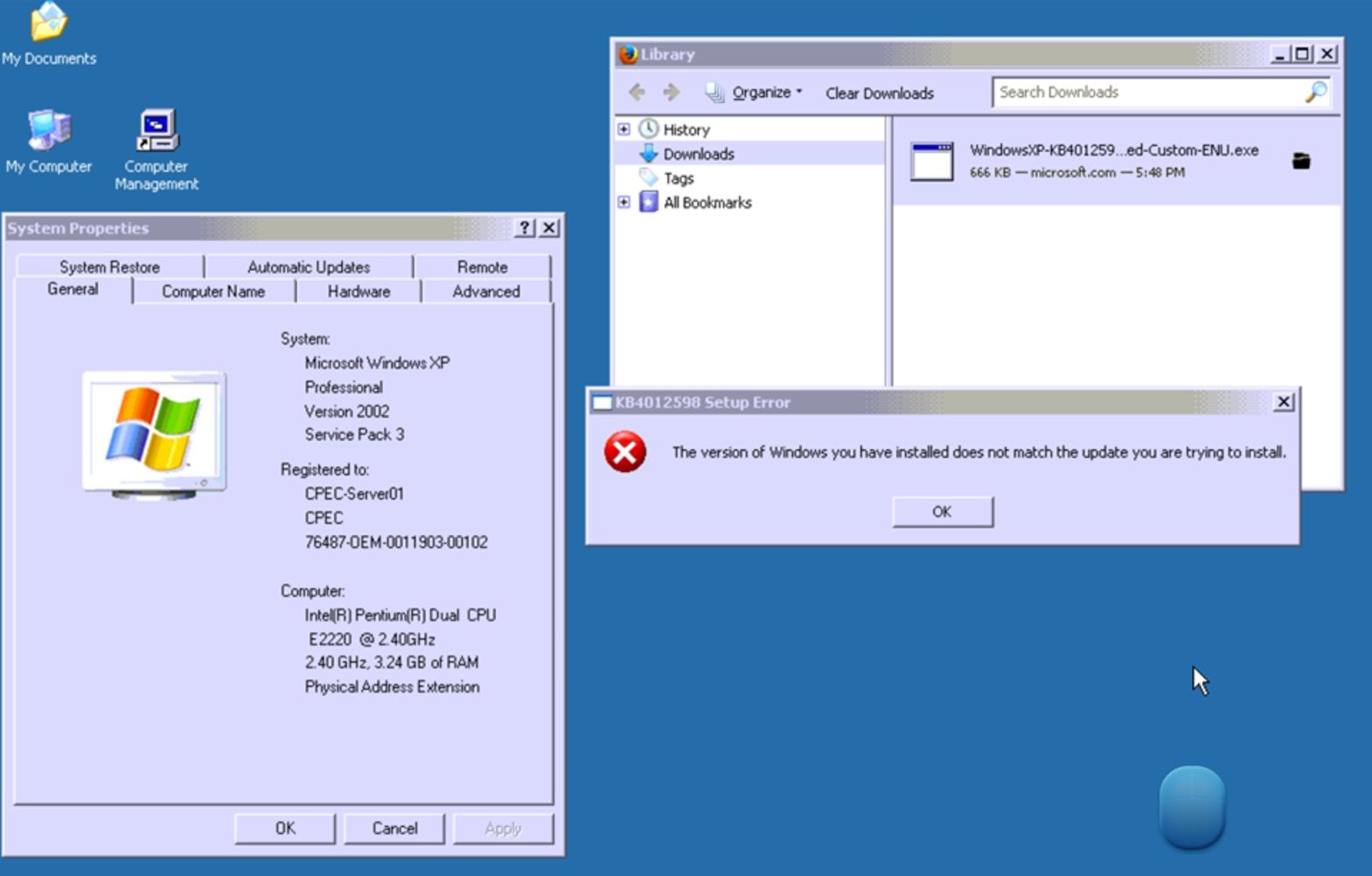
Microsoft just released a patch for Windows XP that fixes a file sharing flaw being exploited by the WannaCry ransomware. Here's how to install it.
You can download some versions of the patch using links at the bottom of this May 12th Microsoft article: Customer Guidance for WannaCrypt attacks. The full list of patch variants, including languages other than English, is in the Windows Catalog, just search for KB4012598.
For an x86 machine with Service Pack 3 installed, the downloaded file name is
windowsxp-kb4012598-x86-custom-enu_eceb7d5023bbb23c0dc633e46b9c2f14fa6ee9dd.exe
I know, its looks like malware itself. The file is small, only 665K. Logon as an Administrator and, for good luck, make a Restore Point first thing.
To see if System Restore is enabled, right click on My Computer, get the Properties and go to the System Restore tab. To actually make the Restore Point, go to Start -> Programs -> Accessories -> System Tools -> System Restore.
The installation process is simple.
1. Wizard warns you to backup your system and close all open programs
2. Then you have to agree to a license
3. Installing the patch takes only a few seconds, even on old hardware. It first asks you to wait while it 'inspects your current configuration, archives your current files and updates your files.' Then it makes a restore point.
4. When its all done, it wants you to reboot
After rebooting, you can verify that the patch was correctly installed using Add or Remove Programs in the Control Panel. You first need to turn on the checkbox to 'Show updates.' Then scroll down looking for the 'Windows XP - Software updates' section. It should be huge.
In this section, look for 'Security Update for Windows XP (KB4012598)' with the current date as the date installed (see above). Considering this is Windows XP, the installation date should stick out like a sore thumb. On two machines that I tested, it was, fortunately, the last entry in the list.
The fix applies to the file sharing component of Windows (Server Message Block or SMB) and thus prevents an XP machine from being infected over a LAN (Local Area Network). However, it would not protect an XP machine that was attacked another way, via email, for example.
I checked around (here and here) and Microsoft has not issued an update to their free anti-malware software, Security Essentials, for Windows XP. When XP went off support, it was denied access to Security Essentials. Thus, XP machines remain vulnerable to WannaCry, just not via file sharing on a LAN.
To fully protect an XP machine requires a third party antivirus product. Lotsa luck with that.
BitDefender bragged today that they can protect against WannaCry, but they do not support Windows XP (see below for update). Neither does Avira, Trend Micro or F-Secure. Kaspersky still supports XP, but their website says nothing about WannaCry.
So, yes, Microsoft released a patch for Windows XP. But now you know the rest of the story.
UPDATE: May 15, 2017. A reader was nice enough to point out that Bitdefender does offer a product that supports Windows XP (and Vista too). The name is fairly direct: Security for XP and Vista.
UPDATE: May 15, 2017. A couple people have told me that when they verified the installation of the patch, the install date was not the current date but tomorrows date. Beats me why.
FEEDBACK
Microsoft Windows Xp Wanna Cry Patch Download Full
Get in touch with me privately by email at my full name at Gmail. Public comments can be directed to me on twitter at @defensivecomput
-->Security Update for Microsoft Windows SMB Server (4013389)
Published: March 14, 2017
Version: 1.0
Executive Summary
This security update resolves vulnerabilities in Microsoft Windows. The most severe of the vulnerabilities could allow remote code execution if an attacker sends specially crafted messages to a Microsoft Server Message Block 1.0 (SMBv1) server.
This security update is rated Critical for all supported releases of Microsoft Windows. For more information, see the Affected Software and Vulnerability Severity Ratings section.
The security update addresses the vulnerabilities by correcting how SMBv1 handles specially crafted requests.
For more information about the vulnerabilities, see the Vulnerability Information section.
For more information about this update, see Microsoft Knowledge Base Article 4013389.
Affected Software and Vulnerability Severity Ratings
The following software versions or editions are affected. Versions or editions that are not listed are either past their support life cycle or are not affected. To determine the support life cycle for your software version or edition, see Microsoft Support Lifecycle.
The severity ratings indicated for each affected software assume the potential maximum impact of the vulnerability. For information regarding the likelihood, within 30 days of this security bulletin’s release, of the exploitability of the vulnerability in relation to its severity rating and security impact, please see the Exploitability Index in the March bulletin summary.
Note Please see the Security Update Guide for a new approach to consuming the security update information. You can customize your views and create affected software spreadsheets, as well as download data via a restful API. For more information, please see the Security Updates Guide FAQ. As a reminder, the Security Updates Guide will be replacing security bulletins. Please see our blog post, Furthering our commitment to security updates, for more details.
| **Operating System** | [**Windows SMB Remote Code Execution Vulnerability – CVE-2017-0143**](http://www.cve.mitre.org/cgi-bin/cvename.cgi?name=cve-2017-0143) | [**Windows SMB Remote Code Execution Vulnerability – CVE-2017-0144**](http://www.cve.mitre.org/cgi-bin/cvename.cgi?name=cve-2017-0144) | [**Windows SMB Remote Code Execution Vulnerability – CVE-2017-0145**](http://www.cve.mitre.org/cgi-bin/cvename.cgi?name=cve-2017-0145) | [**Windows SMB Remote Code Execution Vulnerability – CVE-2017-0146**](http://www.cve.mitre.org/cgi-bin/cvename.cgi?name=cve-2017-0146) | [**Windows SMB Information Disclosure Vulnerability – CVE-2017-0147**](http://www.cve.mitre.org/cgi-bin/cvename.cgi?name=cve-2017-0147) | [**Windows SMB Remote Code Execution Vulnerability – CVE-2017-0148**](http://www.cve.mitre.org/cgi-bin/cvename.cgi?name=cve-2017-0148) | **Updates Replaced** |
| **Windows Vista** | |||||||
| [Windows Vista Service Pack 2](http://catalog.update.microsoft.com/v7/site/search.aspx?q=kb4012598) (4012598) | **Critical** Remote Code Execution | **Critical** Remote Code Execution | **Critical** Remote Code Execution | **Critical** Remote Code Execution | **Important** Information Disclosure | **Critical** Remote Code Execution | 3177186 in [MS16-114](http://go.microsoft.com/fwlink/?linkid=824826) |
| [Windows Vista x64 Edition Service Pack 2](http://catalog.update.microsoft.com/v7/site/search.aspx?q=kb4012598) (4012598) | **Critical** Remote Code Execution | **Critical** Remote Code Execution | **Critical** Remote Code Execution | **Critical** Remote Code Execution | **Important** Information Disclosure | **Critical** Remote Code Execution | 3177186 in [MS16-114](http://go.microsoft.com/fwlink/?linkid=824826) |
| **Windows Server 2008** | |||||||
| [Windows Server 2008 for 32-bit Systems Service Pack 2](http://catalog.update.microsoft.com/v7/site/search.aspx?q=kb4012598) (4012598) | **Critical** Remote Code Execution | **Critical** Remote Code Execution | **Critical** Remote Code Execution | **Critical** Remote Code Execution | **Important** Information Disclosure | **Critical** Remote Code Execution | 3177186 in [MS16-114](http://go.microsoft.com/fwlink/?linkid=824826) |
| [Windows Server 2008 for x64-based Systems Service Pack 2](http://catalog.update.microsoft.com/v7/site/search.aspx?q=kb4012598) (4012598) | **Critical** Remote Code Execution | **Critical** Remote Code Execution | **Critical** Remote Code Execution | **Critical** Remote Code Execution | **Important** Information Disclosure | **Critical** Remote Code Execution | 3177186 in [MS16-114](http://go.microsoft.com/fwlink/?linkid=824826) |
| [Windows Server 2008 for Itanium-based Systems Service Pack 2](http://catalog.update.microsoft.com/v7/site/search.aspx?q=kb4012598) (4012598) | **Critical** Remote Code Execution | **Critical** Remote Code Execution | **Critical** Remote Code Execution | **Critical** Remote Code Execution | **Important** Information Disclosure | **Critical** Remote Code Execution | 3177186 in [MS16-114](http://go.microsoft.com/fwlink/?linkid=824826) |
| **Windows 7** | |||||||
| [Windows 7 for 32-bit Systems Service Pack 1](http://catalog.update.microsoft.com/v7/site/search.aspx?q=kb4012212) (4012212) Security Only[1] | **Critical** Remote Code Execution | **Critical** Remote Code Execution | **Critical** Remote Code Execution | **Critical** Remote Code Execution | **Important** Information Disclosure | **Critical** Remote Code Execution | None |
| [Windows 7 for 32-bit Systems Service Pack 1](http://catalog.update.microsoft.com/v7/site/search.aspx?q=kb4012215) (4012215) Monthly Rollup[1] | **Critical** Remote Code Execution | **Critical** Remote Code Execution | **Critical** Remote Code Execution | **Critical** Remote Code Execution | **Important** Information Disclosure | **Critical** Remote Code Execution | [3212646](https://support.microsoft.com/kb/3212646) |
| [Windows 7 for x64-based Systems Service Pack 1](http://catalog.update.microsoft.com/v7/site/search.aspx?q=kb4012212) (4012212) Security Only[1] | **Critical** Remote Code Execution | **Critical** Remote Code Execution | **Critical** Remote Code Execution | **Critical** Remote Code Execution | **Important** Information Disclosure | **Critical** Remote Code Execution | None |
| [Windows 7 for x64-based Systems Service Pack 1](http://catalog.update.microsoft.com/v7/site/search.aspx?q=kb4012215) (4012215) Monthly Rollup[1] | **Critical** Remote Code Execution | **Critical** Remote Code Execution | **Critical** Remote Code Execution | **Critical** Remote Code Execution | **Important** Information Disclosure | **Critical** Remote Code Execution | [3212646](https://support.microsoft.com/kb/3212646) |
| **Windows Server 2008 R2** | |||||||
| [Windows Server 2008 R2 for x64-based Systems Service Pack 1](http://catalog.update.microsoft.com/v7/site/search.aspx?q=kb4012212) (4012212) Security Only[1] | **Critical** Remote Code Execution | **Critical** Remote Code Execution | **Critical** Remote Code Execution | **Critical** Remote Code Execution | **Important** Information Disclosure | **Critical** Remote Code Execution | None |
| [Windows Server 2008 R2 for x64-based Systems Service Pack 1](http://catalog.update.microsoft.com/v7/site/search.aspx?q=kb4012215) (4012215) Monthly Rollup[1] | **Critical** Remote Code Execution | **Critical** Remote Code Execution | **Critical** Remote Code Execution | **Critical** Remote Code Execution | **Important** Information Disclosure | **Critical** Remote Code Execution | [3212646](https://support.microsoft.com/kb/3212646) |
| [Windows Server 2008 R2 for Itanium-based Systems Service Pack 1](http://catalog.update.microsoft.com/v7/site/search.aspx?q=kb4012212) (4012212) Security Only[1] | **Critical** Remote Code Execution | **Critical** Remote Code Execution | **Critical** Remote Code Execution | **Critical** Remote Code Execution | **Important** Information Disclosure | **Critical** Remote Code Execution | None |
| [Windows Server 2008 R2 for Itanium-based Systems Service Pack 1](http://catalog.update.microsoft.com/v7/site/search.aspx?q=kb4012215) (4012215) Monthly Rollup[1] | **Critical** Remote Code Execution | **Critical** Remote Code Execution | **Critical** Remote Code Execution | **Critical** Remote Code Execution | **Important** Information Disclosure | **Critical** Remote Code Execution | [3212646](https://support.microsoft.com/kb/3212646) |
| **Windows 8.1** | |||||||
| [Windows 8.1 for 32-bit Systems](http://catalog.update.microsoft.com/v7/site/search.aspx?q=kb4012213) (4012213) Security Only[1] | **Critical** Remote Code Execution | **Critical** Remote Code Execution | **Critical** Remote Code Execution | **Critical** Remote Code Execution | **Important** Information Disclosure | **Critical** Remote Code Execution | None |
| [Windows 8.1 for 32-bit Systems](http://catalog.update.microsoft.com/v7/site/search.aspx?q=kb4012216) (4012216) Monthly Rollup[1] | **Critical** Remote Code Execution | **Critical** Remote Code Execution | **Critical** Remote Code Execution | **Critical** Remote Code Execution | **Important** Information Disclosure | **Critical** Remote Code Execution | [3205401](https://support.microsoft.com/kb/3205401) |
| [Windows 8.1 for x64-based Systems](http://catalog.update.microsoft.com/v7/site/search.aspx?q=kb4012213) (4012213) Security Only[1] | **Critical** Remote Code Execution | **Critical** Remote Code Execution | **Critical** Remote Code Execution | **Critical** Remote Code Execution | **Important** Information Disclosure | **Critical** Remote Code Execution | None |
| [Windows 8.1 for x64-based Systems](http://catalog.update.microsoft.com/v7/site/search.aspx?q=kb4012216) (4012216) Monthly Rollup[1] | **Critical** Remote Code Execution | **Critical** Remote Code Execution | **Critical** Remote Code Execution | **Critical** Remote Code Execution | **Important** Information Disclosure | **Critical** Remote Code Execution | [3205401](https://support.microsoft.com/kb/3205401) |
| **Windows Server 2012 and Windows Server 2012 R2** | |||||||
| [Windows Server 2012](http://catalog.update.microsoft.com/v7/site/search.aspx?q=kb4012214) (4012214) Security Only[1] | **Critical** Remote Code Execution | **Critical** Remote Code Execution | **Critical** Remote Code Execution | **Critical** Remote Code Execution | **Important** Information Disclosure | **Critical** Remote Code Execution | None |
| [Windows Server 2012](http://catalog.update.microsoft.com/v7/site/search.aspx?q=kb4012217) (4012217) Monthly Rollup[1] | **Critical** Remote Code Execution | **Critical** Remote Code Execution | **Critical** Remote Code Execution | **Critical** Remote Code Execution | **Important** Information Disclosure | **Critical** Remote Code Execution | [3205409](https://support.microsoft.com/kb/3205409) |
| [Windows Server 2012 R2](http://catalog.update.microsoft.com/v7/site/search.aspx?q=kb4012213) (4012213) Security Only[1] | **Critical** Remote Code Execution | **Critical** Remote Code Execution | **Critical** Remote Code Execution | **Critical** Remote Code Execution | **Important** Information Disclosure | **Critical** Remote Code Execution | None |
| [Windows Server 2012 R2](http://catalog.update.microsoft.com/v7/site/search.aspx?q=kb4012216) (4012216) Monthly Rollup[1] | **Critical** Remote Code Execution | **Critical** Remote Code Execution | **Critical** Remote Code Execution | **Critical** Remote Code Execution | **Important** Information Disclosure | **Critical** Remote Code Execution | [3205401](https://support.microsoft.com/kb/3205401) |
| **Windows RT 8.1** | |||||||
| Windows RT 8.1[2](4012216) Monthly Rollup | **Critical** Remote Code Execution | **Critical** Remote Code Execution | **Critical** Remote Code Execution | **Critical** Remote Code Execution | **Important** Information Disclosure | **Critical** Remote Code Execution | [3205401](https://support.microsoft.com/kb/3205401) |
| **Windows 10** | |||||||
| [Windows 10 for 32-bit Systems](http://catalog.update.microsoft.com/v7/site/search.aspx?q=kb4012606)[3](4012606) | **Critical** Remote Code Execution | **Critical** Remote Code Execution | **Critical** Remote Code Execution | **Critical** Remote Code Execution | **Important** Information Disclosure | **Critical** Remote Code Execution | [3210720](https://support.microsoft.com/en-us/kb/3210720) |
| [Windows 10 for x64-based Systems](http://catalog.update.microsoft.com/v7/site/search.aspx?q=kb4012606)[3](4012606) | **Critical** Remote Code Execution | **Critical** Remote Code Execution | **Critical** Remote Code Execution | **Critical** Remote Code Execution | **Important** Information Disclosure | **Critical** Remote Code Execution | [3210720](https://support.microsoft.com/en-us/kb/3210720) |
| [Windows 10 Version 1511 for 32-bit Systems](http://catalog.update.microsoft.com/v7/site/search.aspx?q=kb4013198)[3](4013198) | **Critical** Remote Code Execution | **Critical** Remote Code Execution | **Critical** Remote Code Execution | **Critical** Remote Code Execution | **Important** Information Disclosure | **Critical** Remote Code Execution | [3210721](https://support.microsoft.com/en-us/kb/3210721) |
| [Windows 10 Version 1511 for x64-based Systems](http://catalog.update.microsoft.com/v7/site/search.aspx?q=kb4013198)[3](4013198) | **Critical** Remote Code Execution | **Critical** Remote Code Execution | **Critical** Remote Code Execution | **Critical** Remote Code Execution | **Important** Information Disclosure | **Critical** Remote Code Execution | [3210721](https://support.microsoft.com/en-us/kb/3210721) |
| [Windows 10 Version 1607 for 32-bit Systems](http://catalog.update.microsoft.com/v7/site/search.aspx?q=kb4013429)[3](4013429) | **Critical** Remote Code Execution | **Critical** Remote Code Execution | **Critical** Remote Code Execution | **Critical** Remote Code Execution | **Important** Information Disclosure | **Critical** Remote Code Execution | [3213986](https://support.microsoft.com/en-us/kb/3213986) |
| [Windows 10 Version 1607 for x64-based Systems](http://catalog.update.microsoft.com/v7/site/search.aspx?q=kb4013429)[3](4013429) | **Critical** Remote Code Execution | **Critical** Remote Code Execution | **Critical** Remote Code Execution | **Critical** Remote Code Execution | **Important** Information Disclosure | **Critical** Remote Code Execution | [3213986](https://support.microsoft.com/en-us/kb/3213986) |
| **Windows Server 2016** | |||||||
| [Windows Server 2016 for x64-based Systems](http://catalog.update.microsoft.com/v7/site/search.aspx?q=kb4013429)[3](4013429) | **Critical** Remote Code Execution | **Critical** Remote Code Execution | **Critical** Remote Code Execution | **Critical** Remote Code Execution | **Important** Information Disclosure | **Critical** Remote Code Execution | [3213986](https://support.microsoft.com/en-us/kb/3213986) |
| **Server Core installation option** | |||||||
| [Windows Server 2008 for 32-bit Systems Service Pack 2](http://catalog.update.microsoft.com/v7/site/search.aspx?q=kb4012598) (Server Core installation) (4012598) | **Critical** Remote Code Execution | **Critical** Remote Code Execution | **Critical** Remote Code Execution | **Critical** Remote Code Execution | **Important** Information Disclosure | **Critical** Remote Code Execution | 3177186 in [MS16-114](http://go.microsoft.com/fwlink/?linkid=824826) |
| [Windows Server 2008 for x64-based Systems Service Pack 2](http://catalog.update.microsoft.com/v7/site/search.aspx?q=kb4012598) (Server Core installation) (4012598) | **Critical** Remote Code Execution | **Critical** Remote Code Execution | **Critical** Remote Code Execution | **Critical** Remote Code Execution | **Important** Information Disclosure | **Critical** Remote Code Execution | 3177186 in [MS16-114](http://go.microsoft.com/fwlink/?linkid=824826) |
| [Windows Server 2008 R2 for x64-based Systems Service Pack 1](http://catalog.update.microsoft.com/v7/site/search.aspx?q=kb4012212) (Server Core installation) (4012212) Security Only[1] | **Critical** Remote Code Execution | **Critical** Remote Code Execution | **Critical** Remote Code Execution | **Critical** Remote Code Execution | **Important** Information Disclosure | **Critical** Remote Code Execution | None |
| [Windows Server 2008 R2 for x64-based Systems Service Pack 1](http://catalog.update.microsoft.com/v7/site/search.aspx?q=kb4012215) (Server Core installation) (4012215) Monthly Rollup[1] | **Critical** Remote Code Execution | **Critical** Remote Code Execution | **Critical** Remote Code Execution | **Critical** Remote Code Execution | **Important** Information Disclosure | **Critical** Remote Code Execution | [3212646](https://support.microsoft.com/kb/3212646) |
| [Windows Server 2012](http://catalog.update.microsoft.com/v7/site/search.aspx?q=kb4012214) (Server Core installation) (4012214) Security Only[1] | **Critical** Remote Code Execution | **Critical** Remote Code Execution | **Critical** Remote Code Execution | **Critical** Remote Code Execution | **Important** Information Disclosure | **Critical** Remote Code Execution | None |
| [Windows Server 2012](http://catalog.update.microsoft.com/v7/site/search.aspx?q=kb4012217) (Server Core installation) (4012217) Monthly Rollup[1] | **Critical** Remote Code Execution | **Critical** Remote Code Execution | **Critical** Remote Code Execution | **Critical** Remote Code Execution | **Important** Information Disclosure | **Critical** Remote Code Execution | [3205409](https://support.microsoft.com/kb/3205409) |
| [Windows Server 2012 R2](http://catalog.update.microsoft.com/v7/site/search.aspx?q=kb4012213) (Server Core installation) (4012213) Security Only[1] | **Critical** Remote Code Execution | **Critical** Remote Code Execution | **Critical** Remote Code Execution | **Critical** Remote Code Execution | **Important** Information Disclosure | **Critical** Remote Code Execution | None |
| [Windows Server 2012 R2](http://catalog.update.microsoft.com/v7/site/search.aspx?q=kb4012216) (Server Core installation) (4012216) Monthly Rollup[1] | **Critical** Remote Code Execution | **Critical** Remote Code Execution | **Critical** Remote Code Execution | **Critical** Remote Code Execution | **Important** Information Disclosure | **Critical** Remote Code Execution | [3205401](https://support.microsoft.com/kb/3205401) |
| [Windows Server 2016 for x64-based Systems](http://catalog.update.microsoft.com/v7/site/search.aspx?q=kb4013429)[3](Server Core installation) (4013429) | **Critical** Remote Code Execution | **Critical** Remote Code Execution | **Critical** Remote Code Execution | **Critical** Remote Code Execution | **Important** Information Disclosure | **Critical** Remote Code Execution | [3213986](https://support.microsoft.com/en-us/kb/3213986) |
[2]This update is only available via Windows Update.
[3] Windows 10 and Windows Server 2016 updates are cumulative. The monthly security release includes all security fixes for vulnerabilities that affect Windows 10, in addition to non-security updates. The updates are available via the Microsoft Update Catalog. Please note that effective December 13, 2016, Windows 10 and Windows Server 2016 details for the Cumulative Updates will be documented in Release Notes. Please refer to the Release Notes for OS Build numbers, Known Issues, and affected file list information.
*The Updates Replaced column shows only the latest update in any chain of superseded updates. For a comprehensive list of updates replaced, go to the Microsoft Update Catalog, search for the update KB number, and then view update details (updates replaced information is provided on the Package Details tab).
Vulnerability Information
Multiple Windows SMB Remote Code Execution Vulnerabilities
Remote code execution vulnerabilities exist in the way that the Microsoft Server Message Block 1.0 (SMBv1) server handles certain requests. An attacker who successfully exploited the vulnerabilities could gain the ability to execute code on the target server.
To exploit the vulnerability, in most situations, an unauthenticated attacker could send a specially crafted packet to a targeted SMBv1 server.
The security update addresses the vulnerabilities by correcting how SMBv1 handles these specially crafted requests.
Windows 8.1 Wanna Cry Patch
The following table contains links to the standard entry for each vulnerability in the Common Vulnerabilities and Exposures list:
| **Vulnerability title** | **CVE number** | **Publicly disclosed** | **Exploited** |
| Windows SMB Remote Code Execution Vulnerability | [CVE-2017-0143](http://www.cve.mitre.org/cgi-bin/cvename.cgi?name=cve-2017-0143) | No | No |
| Windows SMB Remote Code Execution Vulnerability | [CVE-2017-0144](http://www.cve.mitre.org/cgi-bin/cvename.cgi?name=cve-2017-0144) | No | No |
| Windows SMB Remote Code Execution Vulnerability | [CVE-2017-0145](http://www.cve.mitre.org/cgi-bin/cvename.cgi?name=cve-2017-0145) | No | No |
| Windows SMB Remote Code Execution Vulnerability | [CVE-2017-0146](http://www.cve.mitre.org/cgi-bin/cvename.cgi?name=cve-2017-0146) | No | No |
| Windows SMB Remote Code Execution Vulnerability | [CVE-2017-0148](http://www.cve.mitre.org/cgi-bin/cvename.cgi?name=cve-2017-0148) | No | No |
| **Vulnerability title** | **CVE number** | **Publicly disclosed** | **Exploited** |
| Windows SMB Information Disclosure Vulnerability | [CVE-2017-0147](http://www.cve.mitre.org/cgi-bin/cvename.cgi?name=cve-2017-0147) | No | No |
For Security Update Deployment information, see the Microsoft Knowledge Base article referenced here in the Executive Summary.
Acknowledgments
Microsoft recognizes the efforts of those in the security community who help us protect customers through coordinated vulnerability disclosure. See Acknowledgments for more information.
Disclaimer
The information provided in the Microsoft Knowledge Base is provided 'as is' without warranty of any kind. Microsoft disclaims all warranties, either express or implied, including the warranties of merchantability and fitness for a particular purpose. In no event shall Microsoft Corporation or its suppliers be liable for any damages whatsoever including direct, indirect, incidental, consequential, loss of business profits or special damages, even if Microsoft Corporation or its suppliers have been advised of the possibility of such damages. Some states do not allow the exclusion or limitation of liability for consequential or incidental damages so the foregoing limitation may not apply.
Revisions
- V1.0 (March 14, 2017): Bulletin published.
Page generated 2017-05-08 07:15-07:00.